- Business Process Management (BPM)Document Management System (DMS)Electronic Quality Management System (QMS)Risk, Governance & Compliance (GRC)Low Code Rapid Application Development (LC)Business Continuity Management (BCM)Enterprise Architecture (EA)Business Process Management (BPM)Document Management System (DMS)
- Document Control Overview
- AI Content Creation & Improvement
- Policy & Procedure Management (SOP)
- AI Content Mining Parser
- Collaboration & Governance
- Data Migration & Integration
- Interfacing Offline App
 Electronic Quality Management System (QMS)
Electronic Quality Management System (QMS)- Quality Management System Overview
- Document Control & Records Management
- Audit & Accreditation Management
- Corrective & Preventative Action
- Quality Event (Non-conformity / Complaint/ Compliance)
- Risk Management
- Incident Management
- Environmental Health & Safety
- Supplier & Contractor Management
- Product & Supplier Management (SCAR)
- Training Management
- Control Management
- Action Items Management
- Management Review
- FMEA
- Pharmacovigilance
- Data Migration & Integration
 Risk, Governance & Compliance (GRC)
Risk, Governance & Compliance (GRC)- Risk, Governance & Compliance Overview
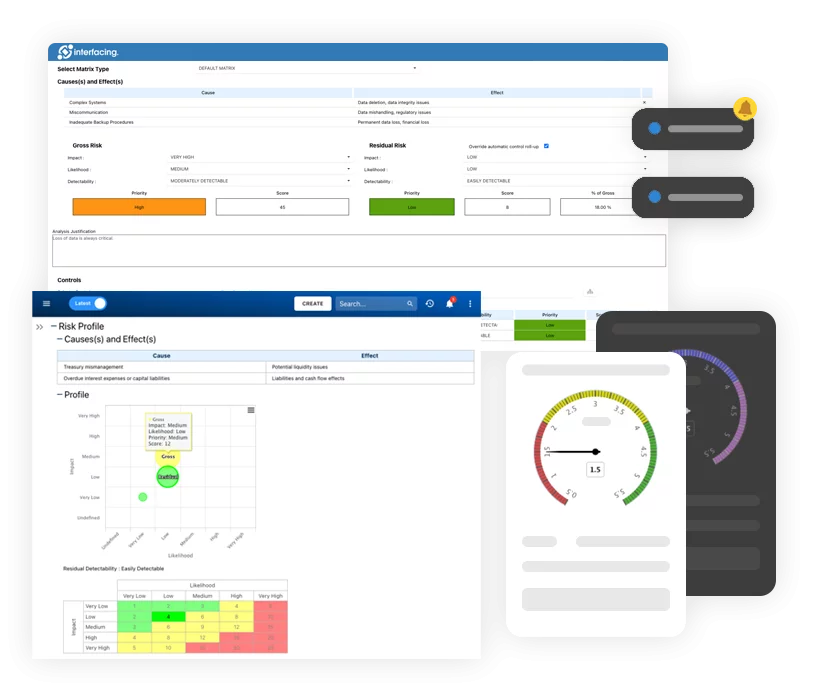
- Risk & Control Management
- Regulatory Compliance
- Collaboration & Governance
- Data Migration & Integration
- Interfacing Offline App
 Low Code Rapid Application Development (LC)
Low Code Rapid Application Development (LC)- Low Code Automation Platform Overview
- Electronic Web Form Design (eFORMS)
- Database Table Entity Designer
- System Integration Designer
- Design & Manage Tasks
- Design & Manage BPMS Apps
- Custom Rules/Guards/Actions
- Electronic Services
- User Homepage
- BAM (Business Activity Monitoring)
- Custom Dashboard Design
- Data Migration & Integration
 Business Continuity Management (BCM)
Business Continuity Management (BCM)- Business Continuity Management Overview
- Business Impact Analysis
- Disaster Recovery Simulation
- Action Item Management
- Mass Notification Management
- Asset Management
- Interfacing Offline App
 Enterprise Architecture (EA)
Enterprise Architecture (EA) - IndustriesRegulatory ComplianceUse CasesLearning CenterFramework & PracticesIndustries
- Healthcare
- Medical Device Technology
- Life Science, Pharmaceutical
- Aerospace & Defense
- Airlines and Aviation
- Media & Telecommunications
- Government and Military
- Technology
- Energy
- Logistics & Port Operations
- Banking & Capital Markets
- Retail & Consumer
- Consulting
- Education
- Engineering & Construction
- Manufacturing
- Financial Services
- Insurance
- Chemicals
Regulatory Compliance- Regulatory Compliance
- ISO
- ISO 9001 (guide)
- ISO 9001:2026 (preparation)
- ISO 17025
- ISO 27000
- ISO 27001
- ISO27002
- ISO 42001
- EU AI Act
- SOC 2 Type 1 & 2
- Sarbanes Oxley
- GxP
- GRC
- Basel
- Digital Signature
- GDPR
- IFRS
- NIST SP 800-53
- MEL in Aviation
 Use Cases
Use Cases- Quality Management System (QMS)
- Digital Transformation
- Continuous Improvement
- Governance, Risk & Compliance
- Knowledge Management
- System Deployment (ERP, CRM…)
 Learning CenterFramework & Practices
Learning CenterFramework & Practices - AboutCustomer SuccessPartners
Comparing SOC2 & ISO27001 Certification
Please Select contact form.
Navigating the Path to Robust Security Compliance

Organizations today are becoming keenly aware of how their vendors and suppliers’ businesses can affect their results. Increasingly, these same organizations are requiring evidenced based documentation attesting to their trustworthiness. One way to prove trust is by the vendors or suppliers to provide a Service Organizational Control (SOC) 2 report.
SOC 2 and ISO 27001: Initial Similarities
Scope
Both ISO 27001 and SOC 2 are designed to provide a level of trust with clients regarding protection of the data they have be entrusted with. In principle, each will cover important aspects of securing their information related to integrity, confidentiality, and availability. When both frameworks are mapped to each other as a comparison, they actually show about 30% of controls overlap. The good news here is that by completing one framework, you have already begun completing criteria of the other
Industry Application
If an organization is selling in the Untied States specifically, both SOC 2 and ISO 27001 would most likely be accepted as a third-party attestation of their information security program. Th only exception would be an outlier within the US government requiring FedRAMP or in healthcare (HIPAA).
Time to Complete
Implementation and evidence collection timelines for SOC 2 and ISO 27001 are very similar provided they follow the three stages of Certification; Gap Assessment/Plan Definition, Implementation/ Evidence Collection and Audit/Certification.
Who defines compliance
Both bodies are independent and reputable, third-party attested certification providers that attest to the security level of an organization
Cost to Complete
SOC 2 and ISO 27001 will be have similar opex costs in terms of internal teams implementing the security controls and evidence gathering needed to prove conformity.
Renewal of Certification
As would be expected with most certifications, in order to remain valid, SOC 2 and ISO 27001 would need to be renewed periodically.
SOC 2 and ISO 27001: Initial Differences
Scope
SOC 2 is a set of audit reports that provide proof of a certain level of conformity to a set of pre-defined criteria (TSC). ISO 27001 on the other hand, establishes the standards for an ISMS (Information Security Management System).
What is its purpose
The intention of SOC 2 is to provide proof of security level achievements of systems against criteria and principles. Alternatively, ISO 27001 adheres to the definition, implementation, operation, control and improvement to overall security.
Industry Application
SOC 2 is geared more towards, service organizations from any industry while ISO 27001 is applicable to any industry of any size.
Who defines compliance
Attestation of SOC 2 is overseen by a licensed Certified Public Accountant (CPA). The certification of ISO 27001 is completed by an ISO certification body.
Geo-location
The SOC 2 standards apply in the United States while ISO 27001 is an established international standard.
Taking a Deep Dive into SOC 2
SOC 2 is a formal set of reports produced as the outcome of an audit. This audit is led by a CPA or a certified accountancy organization.
The contents that make up the reports are defined by the American institute of Certified Public Accountants (AICPA) and as expected, is applicable to U.S. based companies. The SOC 2 certification is designed to validate internal controls of an organization as it relates to information systems that support services that are provided by a company based on 5 quasi-overlapping categories referred to as Trust Service Criteria (TSC).
There is no ‘pass / fail’ objective to the set of reports – the result is a subjective conclusion in-which only the auditor’s opinion is noted on record. Audit reports do not define SOC 2 certification as they are only attested as compliant, based on interpretation by a qualified licensed CPA.
SOC reports come in two types. The Type One reports provide descriptions of an organization’s system of services and that they show if the controls proposed meet or exceed the objectives the organization wishes to achieve. The Type Two report is the same as Type One but also includes attestation that the controls in place operate as described consistently over a period of time (generally about 6 months to a year). A few examples of objectives that need to be achieved include: increase in profitability, decrease in loss or expenses, optimization of operations or fulfilling legal requirements.

What is Trust Service Criteria (TSC)
The five quasi-overlapping categories that work toward the controls used in the SOC 2 reports are:
- Security – Clearly defines that all Systems and Information remain protected against risks that would compromise integrity and impact the organizations’ ability to achieve the objectives outlined.
- Availability – The Systems and Information must always be available anytime they are required in order for an organization to meet and maintain their objectives.
- Processing Integrity – Any processing by the System must only provide trustworthy information at all times when requested / authorized so an organization can meet objectives.
- Confidentiality – In order for an organization to meet its objectives, information can only be accessed by authorized personnel.
- Privacy – personal information must be managed (protected and/or stored) in a certain way that permits the organization to meet objectives.
ISO 27001 and SOC 2 working together
We shouldn’t be asking which of the two frameworks to use simply because SOC 2 is an audit report while ISO 27001 was designed as a standards certification established to create a specific Information Security Management System. This means that SOC 2 can be seen as an output brought on by the delivery of an ISO 27001 ISMS implementation.
The relationship between SOC 2 and ISO 27001 can best be seen as while ISO 27001 is not mandatory in a SOC 2 report, the completion of an ISO 27001 ISMS implementation provides (with little cost and effort) a solid basis for the preparation of the SOC 2 report. Additionally, client confidence and trust is further increased with the use of both frameworks, certified as completed within your organization.


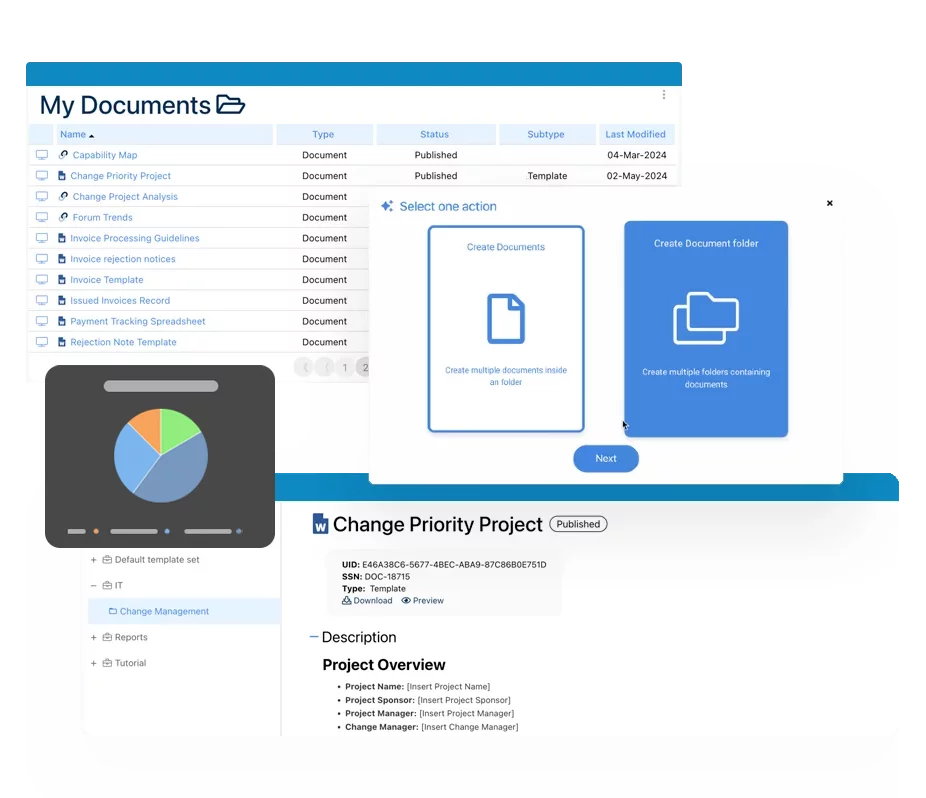
How Interfacing Assists in Easing the Burden of SOC 2 and ISO 27001 Documentation
With the growing complexity of managing SOC 1, SOC 2, and SOC 3 requirements, organizing information in a central location becomes increasingly important. When an auditor comes to the site, they will assess management’s oversight of their third-party service providers as well as the company’s own controls. The majority of this oversight revolves mainly around documentation and the ability to review it.
Interfacing’s IMS platform provides your organization with the ability to capture all equivalency of SOC 1 and SOC 2 requirements (and SOC 3) and match them, where necessary, to ISO international standards (such as ISO 27001 and ISO 9001). This includes running audits and testing to meet SOC compliance, as well as creating test requirements and evidence requests for your internal and external auditors.
Being compliant is just as much about proving this to an auditor as much it is about actually applying the technical controls on your organization, which means providing your auditors with a state-of-the-art quality record management system that can draw on the traceability, accuracy & speed of access to the who, when and how’s of the organizations’ operations objectives.
Interfacing’s Enterprise Process Center® digital platform solution helps you maintain a complete library of:
- Processes
- Procedures
- Roles & responsibilities
- Risks
- All regulatory requirements and standard controls
- Internal policies
- Aligned indicators (KPIs)
- Controlled indicators (Monitoring)
All of the above within a centralized Integrated Management System (IMS) allows your organization to fast-track certification and simplify the creation, communication (new & changes), and update of information security controls, processes, and associated/related documentation.
Additionally, Interfacing’s IMS also offers a Quality Management System for automating the training of your different controls and audits (action item management/CAPA) as well as managing all your documentation, files, processes, procedures, roles, risks & controls.
We offer an entire library of content to jump-start your program or use as a reference library for the operating controls used to validate the maturity of your current ISO 27001 documentation.
Why Choose Interfacing?
With over two decades of AI, Quality, Process, and Compliance software expertise, Interfacing continues to be a leader in the industry. To-date, it has served over 500+ world-class enterprises and management consulting firms from all industries and sectors. We continue to provide digital, cloud & AI solutions that enable organizations to enhance, control and streamline their processes while easing the burden of regulatory compliance and quality management programs.
To explore further or discuss how Interfacing can assist your organization, please complete the form below.

Documentation: Driving Transformation, Governance and Control
• Gain real-time, comprehensive insights into your operations.
• Improve governance, efficiency, and compliance.
• Ensure seamless alignment with regulatory standards.

eQMS: Automating Quality & Compliance Workflows & Reporting
• Simplify quality management with automated workflows and monitoring.
• Streamline CAPA, supplier audits, training and related workflows.
• Turn documentation into actionable insights for Quality 4.0

Low-Code Rapid Application Development: Accelerating Digital Transformation
• Build custom, scalable applications swiftly
• Reducing development time and cost
• Adapt faster and stay agile in the face of
evolving customer and business needs.
AI to Transform your Business!
The AI-powered tools are designed to streamline operations, enhance compliance, and drive sustainable growth. Check out how AI can:
• Respond to employee inquiries
• Transform videos into processes
• Assess regulatory impact & process improvements
• Generate forms, processes, risks, regulations, KPIs & more
• Parse regulatory standards into requirements
Request Free Demo
Document, analyze, improve, digitize and monitor your business processes, risks, regulatory requirements and performance indicators within Interfacing’s Digital Twin integrated management system the Enterprise Process Center®!
Trusted by Customers Worldwide!
More than 400+ world-class enterprises and management consulting firms