What Our Customers Say Matters
Education
Diana R. Associated Teaching Assistant
“Excellent BPM tool and great support. EPC is an excellent tool for creating, executing, and optimizing business processes. The software has valuable functionalities, quite intuitive. The design process and features are flexible and increase visibility into process performance. When I had questions or problems, the Help desk responds rapidly and gives me the necessary support. ”
Technology
Angelo D. Associate Product Manager
“The Digital Business Transformation Suite provides incredible flexibility and scalability, making it perfect for businesses of all sizes. With its advanced features, I was able to develop a digital strategy that was tailored to my business's unique needs.”
Bayer
Armin F. Senior Project Manager and Management Advisor
“Holistic Approach. In opposite to traditional 'specialized' applications like BPM or Document Management, Interfacing is offering in the EPC platform a holistic QMS approach including Risk Management and KPIs. Proven over many industries (Pharma in my focus). ”
Intrust Bank
Jessica H. Business Analyst - Project Management
“Endlessly Flexible and Functional. As a Business Analyst, I love how I can tie everything together and present the same information in varying levels of detail. I can model technical requirements that roll up into pretty user interface stories with very little effort. I also love the flexibility and allows other teams to use it the way they need it. It's so powerful. ”
Quebec based company
Guillaume A. Business Analyst
“Good tools, well-suited, and available in French - made right here in Quebec. The solution is available in French, made in Quebec, and includes multilingual content management features. There are also process analysis tools, simulation, and a suite for audit and CAPA management. ”
Saudia Airlines
Ahmad S., Maintenance Engineer
“This tool provides the best of both world, easy to use along with powerful features. It is the only tool that supports content in Arabic, and we were very well supported during our project. To be honest, other tools made promises about their systems that we could not verify in the testing phase. Interfacing's did correspond to what we were ultimately looking for. ”
Orange
Martine P., Operations Manager
“The platform is powerful and enables collaboration, and reuse. For us, reusing processes, content, tasks, is critical in building a more agile and resilient model. Interfacing has been very diligent and reactive in supporting our model. ”
Pepsi-Cola
Control Officer Team, Pepsi-Cola
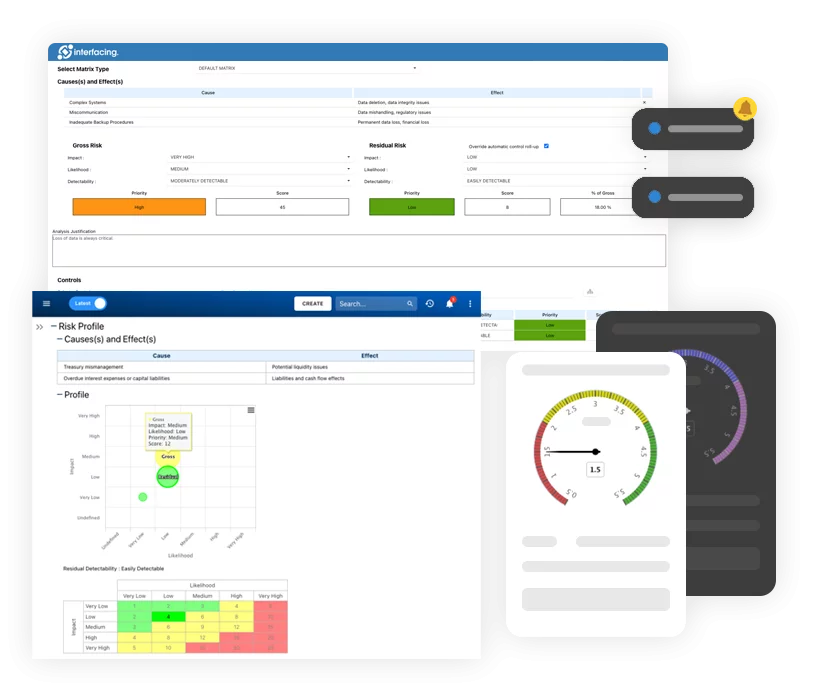
“Our auditors gave us excellent feedback on the use of the EPC as part of our GCS implementation initiative. They were particularly impressed with our ability to identify controls and relate them to risks prioritized with the Risk Matrix. They have since recommended our approach to internal GCS compliance as best-practice for other PepsiCo plants.”
Price water house Coopers
Alfonso Velázquez Tavira, PWC BAS Manager, PricewaterhouseCoopers
“EPC’s competitive licensing pricing will allow us to deploy the software to about 36,000 expected end users across Mexico in the next two years. We chose EPC over Bizagi BPM, Fuego BPM and Microsoft Biztalk Server because of its wide range of integrated functionality when it comes to process mapping and automation. All of the BPM suites we considered had functionalities that didn’t meet UNAM’s present needs. With Enterprise Process Center (EPC) we chose which modules we needed to address the problems we were facing currently, with the flexibility to extend in the future as UNAM’s process maturity grows.”
Prospera
Michelle B, Technical Writer
“I like that everything can be linked to a process. I like that you can view processes via a process map or detailed format. Great support during planning phase and project manager worked with our team during development. Any questions we had during the project were answered promptly and if we have questions now, we reach out to the support team.”
Qnet
Oscar M. Erickson, Information Technology Services Specialist
“The best application for management This system is simple and easy to use with unique features that make this application a vital tool for any management of any company, thanks to its integral functions allows to have a complete overview of the performance of each area of the company, has a friendly interface that facilitates its use and adaptability quickly and safely.”
Rema Tip Top
Corey Lynch, Business Improvement & Compliance Manager, Rema Tip Top
“The automated monitoring feature of the SOP module bridges the gap between ongoing process management and procedural associated documents and is a great aid for compliance purposes, which constantly require up to date information.”
Orange
Jean-Luc Heloin, Project Director, Orange Business Services
“EPC was the only tool that answered the project’s needs and requirements. We are rolling out corporate-wide to over 300 modelers & 120K employees!”
Royal Australian Air Force
Warren Harrison, Business Improvement Manager, Royal Australian Air Force
“The EPC allowed our people to show their processes in an easy to understand format. It fits perfectly with the ISO process approach. Auditors understood the method very easily.”
San Francisco Public Utilities Commission
Andrea Pierce, Business Applications, San Francisco Public Utilities Commission
“Enterprise Process Center is easy to use, requiring little or no training for rollout, therefore, lowering resistance especially by our non-tech employees. It also allows us to easily train new employees with the knowledge relevant to their roles and responsibilities.”
SGI
Laura - Executive Sponsor in Insurance
“Excellent tool supported by a great team The tool itself is great – for more robust than what I initially imagined. What I like best is that there is a team at Interfacing that supports us in establishing best practices for using the tool. We are using Interfacing to document the dependencies from an architecture stand point, as well, to do analysis on process models.”
Stuart Wright Pte Ltd.
Colin Stuart, Senior Well Engineer, Stuart Wright Pte Ltd.
“In the midst of working on a project, any of us well engineers may require replacement for a number of reasons. The replacement engineer will be thrown in the middle of a project, and may not be able to understand the project state. However, with the help of the EPC process maps, the replacement will be able to quickly gain a clear understanding of the project. He just has to know where the work left off and look in the EPC to follow-up on the next step. As such, it doesn’t matter who the person is doing the work; as long as the process is mapped out, the skills are there, and any relevant person can follow through on the entire project. We have found the right tool to make our company a leading-edge consulting engineering business; we even incorporated EPC process shapes in our logo.”
Tennant Company
Tennant Company Team
“We are very impressed with EPC’s functionality and ease of use. We look forward rolling this out across our enterprise.”
Unisys
Mike Hutchinson, VP & General Manager of IMS Worldwide, Unisys
“Our search produced approximately 35 companies that looked promising. After further review, we eventually eliminated most, and finally selected Interfacing’s FirstSTEP technology as the one most suited to our initial needs. Enterprise Process Center has helped us roll out a process-based methodology globally so our people provide consistent service and support no matter where in the world. We believe this product has given us a significant competitive advantage while improving relationships with our clients.”
'US' Utility Services
US Spokesperson, 'US' Utility Services
“A key component of the initiative, and a primary tool for the CoE and the business, in general, was a powerful technology that allowed us to model in a collaborative environment and easily validates the work with process owners. Using the Interfacing’s Enterprise Process Center® (EPC), we modeled processes from both an enterprise-wide, value stream perspective and from the day-to-day task perspective. This was crucial not only to our analysis but also for showing value, sustaining executive support and for validating our work with process actors and owners.”
Veridata Networks
Roehl G. Fontanilla, Vice President, Veridata Networks
“Business will always look for ways to improve their processes, but the biggest challenge is to know where to start and how! EPC provides the capability to see the relationships among these processes in a holistic perspective; providing a clear view of areas where improvements can deliver efficiency and realize cost savings.”
Alexandru Ioan Cuza University
Laura-Diana Radu, Lecturer Phd
“The software has valuable functionalities, quite intuitive. The design process and features are flexible and increase visibility into process performance. When I had questions or problems, the Help Desk responds rapidly and gives me the necessary support.”
Azelis
Jeremie Lauzier, ICT Manager
“Really good to produce SOP The product is Online, no software to install and it is powerful. We make better SOP, we have better communication of new processes and a better understanding of the processes.”
Bombardier
David Orcutt, VP & General Manager of Programs and Customer Support, Bombardier Aerospace
“We have been working with since July 1998. Integrating business units, by aligning practices between different sites, has been facilitated by being able to link all our processes into one integrated framework shared by all managers. We are counting on FirstSTEP® to enable us to simulate anticipated business volumes and efficiently prepare for and manage our growth with tailored action plans.”
E&Y Central America Inc.
Pablo Arrieta, Partner Advisory Services, E&Y Central America Inc.
“Even if we are aware of other companies that compete with Interfacing we have partnered with them not only because they provide a very competitive set of solutions but also because of a relationship built on trust, collaboration and values that have been tested in the good times but also in the difficult ones.”
Equifax
Global Technologies Operations Office, Equifax
“EPC is robust, intuitive and highly collaborative. EPC is an integral tool to enable the delivery of our Global Service Management Strategy.”
Exelon Power Team
Blake McLaughlin, Senior Project Manager, Exelon Power Team
“Our modeled processes not only served as a strong backbone to our division’s business plan but also empowered all of us to take ownership of our activities and performance.”
International Air Transport Association (IATA)
Sara ARROUN, Senior Manager Quality & Process Improvement
“Great Service and strong relationship I like how responsive the team is, how fast in providing solutions, and how friendly and approachable they are. They provide support in everything ranging from technical issues to process modeling support when I am not able to figure out certain features. I always get my questions answered. The Live Chat is a great channel.”
ICF
Allan Bachan, Vice President
“EPC is very flexible; intuitive; and little training is required. I am u sing EPC for several consulting projects: Solution Blueprinting for IT projects; Performance Measurement and Management Projects; Operations improvement projects.”
Microsoft
Hisashi Sato, Senior Product Manager Microsoft
“[Interfacing’s BPMN Modeler] gives business users the ability to create sophisticated business models with the ease-of-use that Visio is famous for. It allowed me to create connections between flowcharts and build a multi-leveled process framework in minutes.”
Moreland City Council
Bernard Hoehmann, Business Solutions Architect
“Professional company and very competitive Interfacing are able to construct an implementation plan that completely adapts to our needs. The product is highly configurable. I strongly recommend that you consider Interfacing when testing the market. We will create a process library of our business. We also need to construct a framework that relates business processes to risks, costs, owners and approvers.”